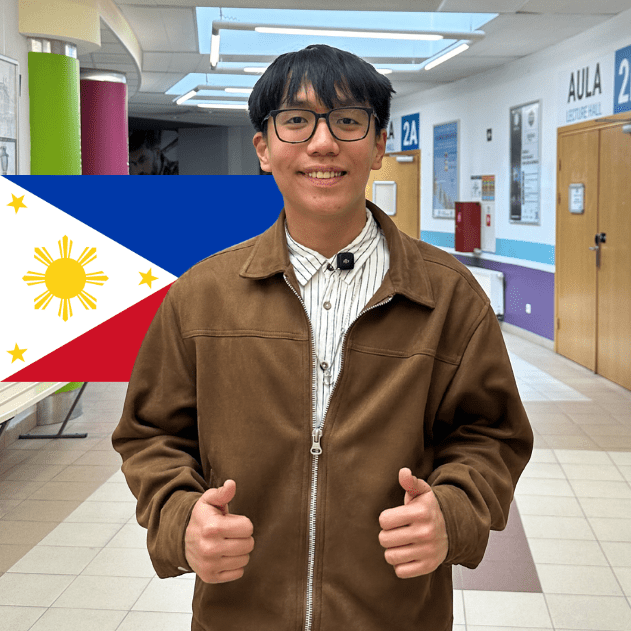
Yuri
Philippines | Computer Engineering BA Yuri from the Philippines combines innovation with student life as a member of the robotics team…
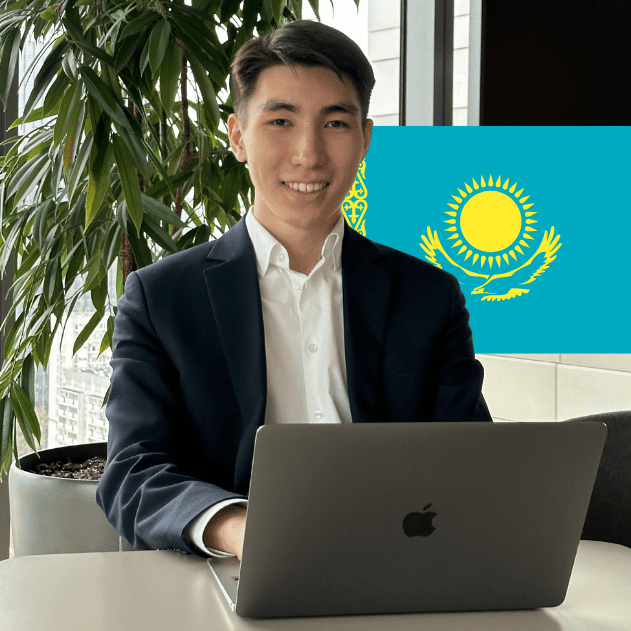
Aldiyar
Kazakhstan | Finance and Accounting with ACCA Aldiyar from Kazakhstan pursued a degree in Finance and Accounting with ACCA at Vistula…
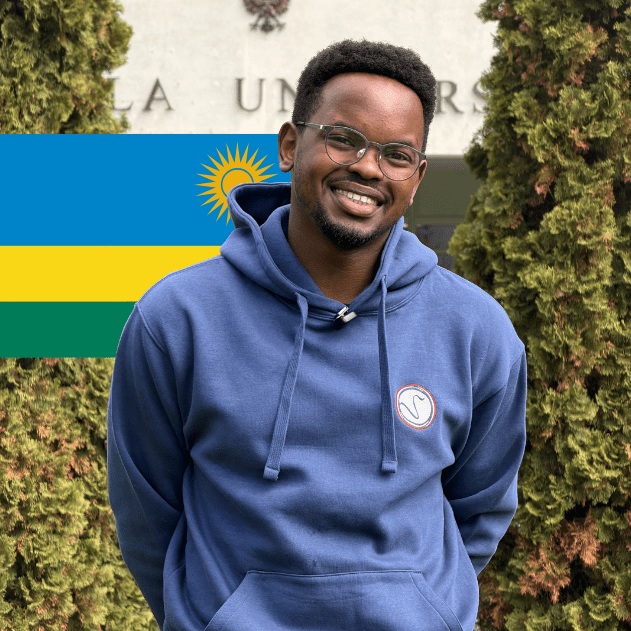
Prince
Rwanda | Management (MA) Prince from Rwanda is an active student ambassador and a Master’s student in Management at Vistula University.

Nimo
Ethiopia | Artificial Intelligence BA Nimo from Ethiopia is a talented Computer Engineering student and an active member of the robotics…

Bry
United States | Tourism Management (BA) Bry from the United States crossed the ocean to experience student life in Europe and…

Ilona
Ukraine | Finance and Accounting with ACCA Ilona from Ukraine graduated in Finance and Accounting with ACCA and successfully transformed her…
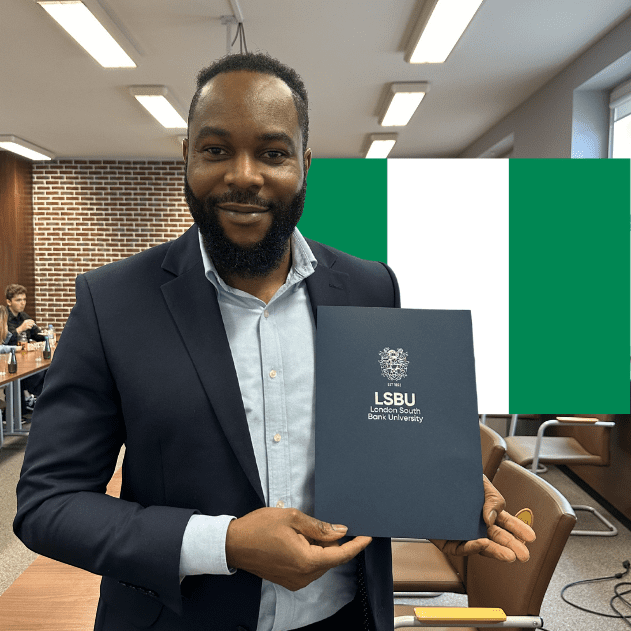
Happy
Nigeria | Double Degree Program in Management Happy Johnson from Nigeria completed both his Bachelor’s and Master’s degrees in Management at…

Ivana
Venezuela | International Relations (BA) Ivana from Venezuela earned a Vistula Merit Scholarship and became an active ambassador of the university community. Studying…
